Next-Gen Email Security
Stop advanced email attacks before they reach users. Our autonomous AI agents detect, adapt, and respond to new threats in hours, giving teams full visibility and control on demand.
.avif)









.svg)



.svg)


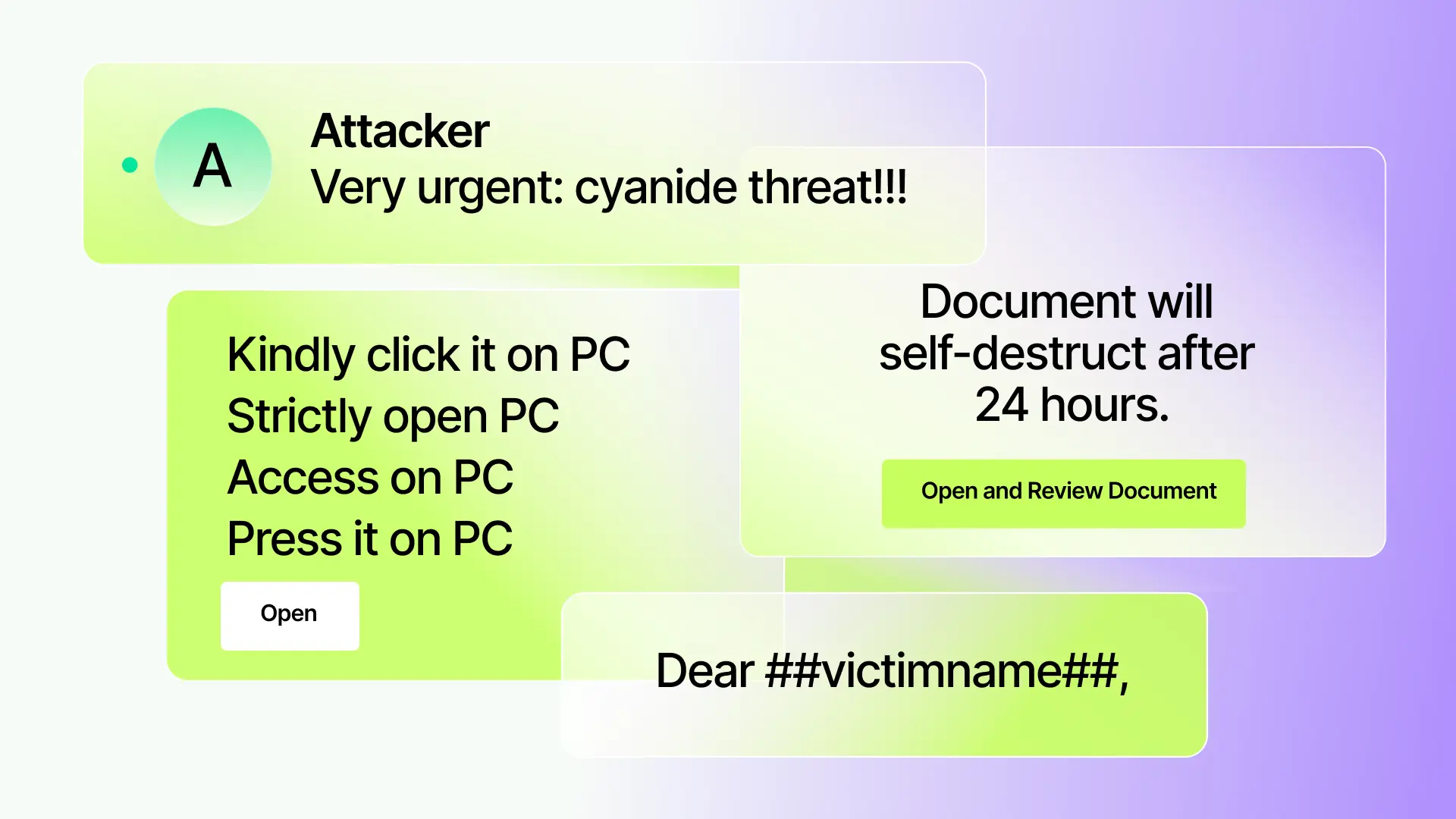
Legacy security solutions can’t keep up with AI-powered attacks
One size doesn’t fit all
Static detection can't adapt to rapidly evolving, AI-powered tactics.
Limited transparency
Opaque verdicts leave you guessing why attacks are caught or missed.
Recurring false positives
False positives drain analyst hours and disrupt the business.
Vendor bottlenecks
Waiting months for vendors to fix false positives or missed attacks slows your response.
An agentic defense, automatically tailored to you
Sublime is the next generation of email security.
Our platform deploys a team of specialized AI agents that autonomously stop targeted attacks, delivering superior efficacy while eliminating busywork for your team.
ASA

Autonomous Security Analyst
Instantly triages user-reported emails, clearing your abuse mailbox and freeing up your analysts.
.avif)
.avif)
ADÉ

Autonomous Detection Engineer
Proactively authors new, backtested detections for emerging threats, ready for your one-click approval.
How Sublime delivers better email security
Sublime empowers security teams with tailored detections, explainable alerts, and automation - so you can prevent, detect, and respond to threats faster and with confidence.
Stop more attacks with fewer false positives
Block sophisticated threats like BEC and novel phishing with a higher catch rate, and fewer workflow-breaking false alarms.
Learn more
See why every decision was made
Every action Sublime takes is backed by matched detections, signal analysis, and clear evidence you can trust.
Learn more
Adapt defenses automatically
When a novel attack is identified, ADÉ generates backtests, and deploys new org-specific coverage in hours, not months
Learn more
Evolve beyond just the vendor black box
Full transparency into every decision
See the reasoning for every detection and result.
Independence from vendor bottlenecks
Deploy your own org-specific detections without waiting on vendor queues.
Tailored coverage that evolves
AI agents author, backtest, and deploy new detections in hours, not months.
Don’t take our word for it
.svg)

Sublime gives us the ability to use our email security solution across the organization in ways we previously couldn't. It is easy, effective, and evolves with the threat landscape.
Haider Dost
Head of Global Threat Detection and Threat Intelligence
Latest from Sublime
Two ways to try Sublime for free
Quickly protect your email environment with Sublime’s free email security tools. Create an account or analyze an email right away.
.svg)
Analyze an email
Scan and analyze suspicious emails with advanced email protection tools.
Get actionable insights into email threats.
Preview suspicious links and identify phishing attempts.
.svg)
Get started with Sublime
Start with Enterprise to evaluate the full platform.
Deploy fast and scale confidently, from early-stage teams to complex enterprise environments.
Autonomous, AI-powered email security that adapts to new threats.
Frequently asked questions
What is email security?
Email security refers to protective measures that prevent unauthorized access to email accounts and protect against threats like phishing, malware, and data breaches. Modern email security like Sublime use AI-powered technology to detect and block sophisticated attacks while providing visibility and control over your email environment.
What is the best email security?
The best email security adapts quickly to emerging threats and minimizes false positives. Sublime Security offers an adaptive platform that combines AI-powered protection with unprecedented visibility and control. It detects advanced threats like GenAI-powered phishing attacks and provides comprehensive protection for cloud-based email environments.
What are the main challenges in modern email security?
Modern email security faces challenges from GenAI-powered spear phishing campaigns, cloud-based payload obfuscation, and rapidly evolving attack techniques. Traditional solutions struggle to keep pace with these threats. Advanced email security platforms must adapt quickly, reduce false positives, and provide comprehensive visibility to address these evolving challenges.
How does AI improve email security?
AI enhances email security by detecting sophisticated phishing attempts that evade traditional defenses. It extracts detection signals, generates potential coverage, and backtests through layers of protection. AI-powered platforms like Sublime can adapt to new threats in hours or days rather than months, providing more responsive protection against evolving attacks.
What features should I look for in email security?
Look for email security that offer adaptive protection against emerging threats, minimize false positives, provide comprehensive visibility, and include incident response capabilities. The solution should protect against sophisticated phishing, insider threats, and GenAI-powered attacks while offering search capabilities for suspicious messages and actionable threat intelligence.
How does cloud-based email security differ from traditional options?
Cloud-based email security offer greater scalability, faster updates, and better protection against modern threats than traditional options. They provide real-time threat intelligence, automated response capabilities, and protection against cloud-specific threats like obfuscated payloads. Solutions like Sublime are specifically designed to address the unique security challenges of cloud environments.
Now is the time
See how Sublime delivers autonomous protection by default, with control on demand.
.avif)

.svg)